What Is a DNS Leak Test? How to Prevent VPN Leaks in 2026
A DNS leak occurs when a VPN accidentally forwards unencrypted traffic, showing your real IP address. To run a DNS leak test, simply check your IP address before and after connecting to a VPN server. My favorite choice, NordVPN, passes every time — you can try it for free with a 30-day money-back guarantee.
If you plan to use a virtual private network (VPN) to keep yourself safe on the internet, knowing how to run a DNS leak test is critical. It’s as important as drivers knowing how to change a tire or cooks understanding how to put out a grease fire.
A DNS leak is a security flaw in some VPNs that can reveal your online activity to your internet service provider (ISP) while you supposedly have VPN protection. Any privacy-conscious person should avoid DNS leaks at all costs.
- Best leak-proof VPN
In this article, I’m going to walk you through the steps of performing a DNS leak test, the types of leaks you should be aware of and the DNS leak fix in case you find one.
What does it mean if your DNS is leaking?
It means that your web browser is contacting DNS servers outside the protected VPN tunnel created by your VPN. This could be because your ISP is using transparent proxies or your VPN service doesn’t have an airtight server network. Either way, your best response is to find a new VPN.What is a DNS test?
A DNS test checks to see if your VPN is resolving all requests using safe, encrypted servers, and not inadvertently revealing your IP address. You can use ipleak.org, browserleaks.com or dnsleaktest.com to run a test for free, but make sure you know your real IP address first.
How Do You Perform a DNS Leak Test?
In the section below, I’ll get more into how a DNS leak occurs and what it actually is. However, you don’t need any technical knowledge to perform a DNS leak test. For now, just know that a DNS leak is a security flaw that keeps a VPN from doing its job.
DNS leaks are most common on VPNs that haven’t sufficiently tested their security, especially those that primarily use rented or virtual servers. No VPN is free of the possibility, though. Zero-day vulnerabilities or operating system flaws can spring a leak in an otherwise airtight server network.
For that reason, you should test for DNS leaks at least once a month by following these steps.
1. Find out your IP address
To start, you’ll need to know your real IP address — that is, what your ISP and everyone else sees when you’re not protected by a VPN server. Turn off your VPN and anything else that might mask your IP address. Then go to whatismyipaddress.com. Take note of the IP address shown, along with your ISP and physical location.
2. Connect to the VPN you’re testing
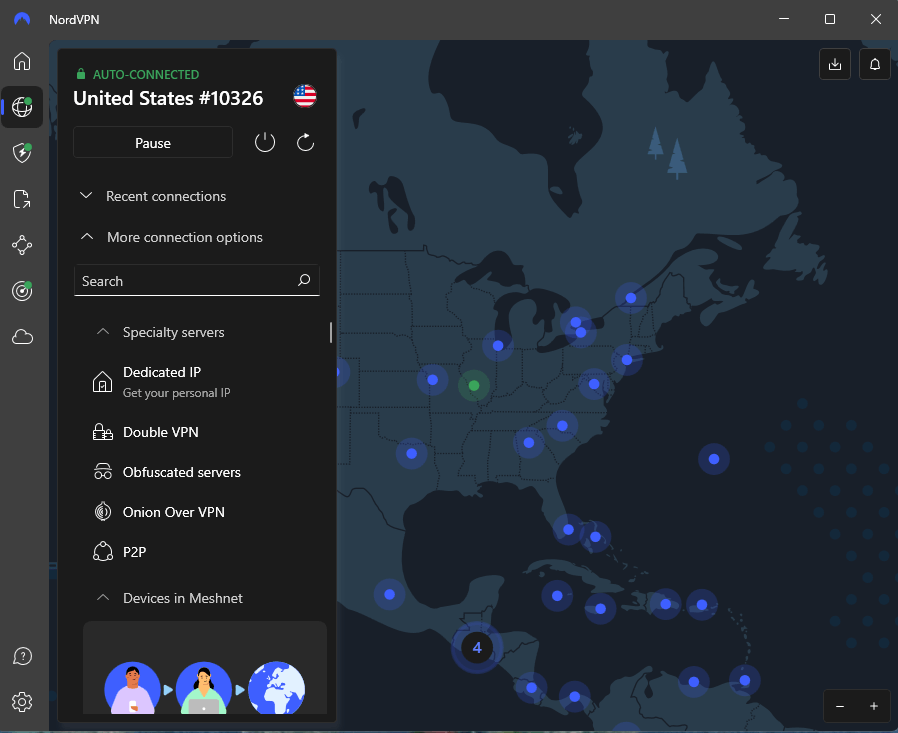
Access the VPN and connect to a server. For the test, choose a server location outside your city. This will make the results easier to interpret.
3. Go to a leak test website
I recommend ipleak.org or dnsleaktest.com, though any site will work as long as it’s not attached to the VPN being tested. Alternatively, you can use whatismyipaddress.com again. There’s little functional difference between an IP address lookup site and a DNS leak tester.
4. Compare the IP address and location to your unprotected status
If the address or location are the same as they were in step one, you’ve identified a DNS leak. Stop using that VPN, and consider reporting the vulnerability. But if the page shows the IP address and location of your VPN server, congratulations: your VPN is in good working order.
How Does a DNS Leak Test Work?
A site like dnsleaktest.com tests your VPN service by asking it to look up several websites, the same way it looks up any website you want to view. The VPN resolves the domains and connects them back to your device.
The leak test then checks to see if any of the domains are using your real IP address, rather than your address encrypted by the VPN tunnel. If your real address ever appears, then you likely have a DNS leak on your hands.
What Is a DNS Leak?
In the old days of the internet, the only way to connect to a website was through the IP address of its server. You had to remember a long sequence of numbers and key it in every time.
That changed with the introduction of the domain name system (DNS). Without getting too technical, DNS is a registry of domains represented by URLs, each of which is linked to a server IP address. A DNS server maintains the knowledge required to match IPs with URLs.
Whenever you want to view a web page, your browser sends a request to a DNS server, which looks up the IP associated with the domain name you entered. These requests are called DNS queries, and the resulting information is called “resolving” a domain name.
Using a VPN adds an extra step to this process. Your browser sends DNS queries to the VPN, which resolves it using trusted, anonymous DNS servers operated outside ISP authority. That keeps everything safely inside an encrypted VPN tunnel.
A DNS server leak occurs when DNS queries bypass the anonymous DNS servers and resolve using the same servers they always would, sending the information back to your real IP address. Your address is then visible to your ISP, along with anyone else who might be looking.
Top Reasons for DNS Leaks
Since the main reason to use a VPN is to conceal your real IP address, DNS leaks are a huge problem. Fortunately, they’re rare on the top best VPNs. Below are a few of the most common reasons for a DNS server leak.
VPNs that don’t own their servers
A VPN is relatively easy to develop. The hard part is building a server network that offers DNS leak protection. Some newer VPNs take a shortcut by renting server time instead of owning their own data centers. Without full control over the servers, they can’t guarantee DNS requests will resolve anonymously.
VPNs that don’t support IPv6
IPv6 is a newer, more expansive format for IP addresses. The internet is still transitioning to IPv6 from the older IPv4 standard, and some VPNs haven’t caught up (see “IPv6 Leaks” below).
ISPs using transparent proxies
Some ISPs are countering VPNs by using proxies that force all connections onto DNS servers operated in the ISP’s networks. In effect, they’re forcing you to let DNS requests leak before you can use the internet. A reliable VPN connection can circumvent these proxies, but some services will buckle and leak your IP.
Windows operating system features
Two Windows features — “Smart Multi-Homed Name Resolution” (SMHNR) and Teredo — can cause DNS leaks while they’re active. If you detect a leak, check to make sure you have these features turned off, then try the test again.
Other Leaks to Watch Out For
DNS leaks aren’t the only leaks you have to worry about, unfortunately. A VPN might also have WebRTC leaks or IPv6 leaks.
WebRTC Leaks
Much like DNS, WebRTC is a universally accessible tool that helps make the modern internet as convenient as it is. RTC stands for “real-time communications,” a name that tells the story: through the WebRTC plugin, sites can transmit audiovisual information in real time without either side having to download additional software.
Also, like DNS servers, the convenience of WebRTC comes with risk. The plugin establishes a two-way connection, allowing the other website to request your real IP address. Many VPN services weren’t prepared for this when WebRTC first launched, but over the past decade, the best providers have found ways to make WebRTC safe to use.
Testing for a WebRTC leak is a lot like testing for a DNS leak. The website browserleaks.com has a designated WebRTC leak test. To use it, follow the same steps listed above.
IPv6 Leaks
As the internet boomed, computer scientists began to fear that the IPv4 system would run out of available addresses before long. IPv6 is the solution, providing such a large number of possible domains that it’ll be hard to run out before the sun swallows us.
The problem is that most of the technology that undergirds the internet was developed around IPv4 addresses. That includes VPNs. Many services were designed to protect IPv4 traffic, and without additional retrofitting, might let traffic involving an IPv6 address run freely through DNS servers.
Most ISPs now assign IPv6 addresses at least some of the time, so this security hole is only going to grow. Fortunately, some VPNs are responding to the problem. There are two general approaches to stopping IPv6 leaks.
A. Rebuild VPN Code
The first is to rebuild the VPN’s code, so it can handle both IPv4 and IPv6 traffic. This is less common, but some VPNs have pulled it off, including CyberGhost and AirVPN.
B. Block IPv6 Addresses
The other approach is to simply block IPv6 addresses entirely. At the moment, very few websites support only IPv6, so this shouldn’t be a problem — you’ll just continue to communicate with IPv4 addresses. VPNs that choose this approach include NordVPN, ExpressVPN, and Private Internet Access.
If you prefer a VPN that has no IPv6 plan whatsoever, you aren’t out of luck; just disable IPv6 from your operating system. No matter what VPN you use, run regular leak tests. The method described above is effective for both IPv4 and IPv6 addresses.
Conclusion: Prevent DNS Leaks
DNS leaks are like any other risk of living life online. You shouldn’t live in fear, but you can take common-sense precautions against revealing yourself to DNS servers. As long as you’re using a well-regarded VPN service with DNS leak protection and conduct regular tests, you can keep browsing safely.
Have you ever suffered a DNS leak? What did you do about it? I’d love to hear your story in the comments. As always, thank you for reading!

Leave a Reply